

A special committee headed by Prime Minister Benjamin Netanyahu’s chief of staff, Harel Locker, has recommended a three-phase plan to all but do away with cash...

Pope Francis extolled the benefits of sharing wealth with the poor on Tuesday, warning that "unjust" social conditions like unemployment can lead to sin, financial ruin...


The onslaught of technological coolness is dazzling, mind-boggling even. Everywhere you look there are apps and wearable devices that sync up to the cloud, and everyone...

Bitcoin is not just a digital currency, like the dollar or the yen or the euro. It’s also a payment system, like PayPal or the Visa...
Obama first step was to get millions and millions of Americans wholly dependent on government entitlements like welfare and food stamps. Now we have his second...

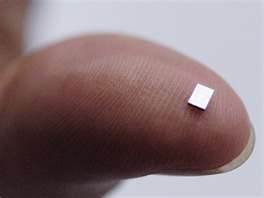
For some time now, scientists have been working on the fusion of human beings and computer-controlled machines known as singularity. Computer chip giant Intel Labs has...
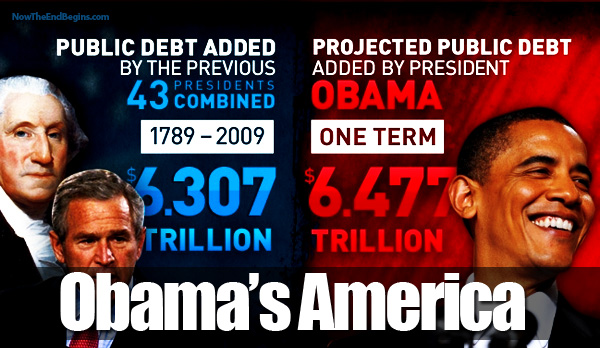
Lew again warned that President Barack Obama would not negotiate with Republicans over the debt limit.
The U.S. Department of Homeland Security will test its crowd-scanning facial recognition system, known as the Biometric Optical Surveillance System, or BOSS, at a junior hockey...


"All of that stuff" - meaning every telephone conversation Americans have with one another on US soil, with or without a search warrant - "is being...
The next time you update your iPhone software, Apple will be able to track you down to the exact corner of the room you are in.


Futurists have long proclaimed the coming of a cashless society, where dollar bills and plastic cards are replaced by fingerprint and retina scanners smart enough to...
The USDA is now considering biometric identification for all individuals who will want to benefit from their Food and Nutrition Services. Biometric identification technology provides automated...

Take a look at the green stuff in your wallet and prepare to say goodbye to it in the future: By 2020, most Americans will be...


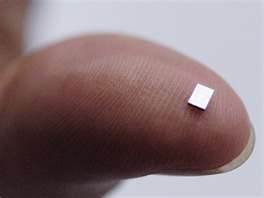
Broadcom has just rolled out a chip for smart phones that promises to indicate location ultra-precisely, possibly within a few centimeters, vertically and horizontally, indoors and...

The Canadian government has announced that it will stop distributing the Canadian penny beginning in the fall, with the gradual goal of removing it from circulation....


In most Swedish cities, public buses don't accept cash; tickets are prepaid or purchased with a cell phone text message. A small but growing number of...