Headline News
Russians Hack Obama White House Computer Network In ‘Spear Phishing’ Attack
Director of National Intelligence James Clapper told a Senate hearing in February that the “Russian cyber-threat is more severe than we have previously assessed.”

To get to the White House, the hackers first broke into the State Department, investigators believe.
Washington, DC – Russian hackers behind the damaging cyber intrusion of the State Department in recent months used that perch to penetrate sensitive parts of the White House computer system, according to U.S. officials briefed on the investigation.
While the White House has said the breach only ever affected an unclassified system, that description belies the seriousness of the intrusion. The hackers had access to sensitive information such as real-time non-public details of the president’s schedule. While such information is not classified, it is still highly sensitive and prized by foreign intelligence agencies, U.S. officials say.

Director of National Intelligence James Clapper told a Senate hearing in February that the “Russian cyber-threat is more severe than we have previously assessed.”
The White House in October said it noticed suspicious activity in the unclassified network that serves the executive office of the president. The system has been shut down periodically to allow for security upgrades.
The FBI, Secret Service and U.S. intelligence agencies are all involved in investigating the breach, which they consider among the most sophisticated attacks ever launched against U.S. government systems. The intrusion was routed through computers around the world, as hackers often do to hide their tracks, but investigators found tell-tale codes and other markers that they believe point to hackers working for the Russian government. A spokesman for the National Security Council declined to comment. Neither the U.S. State Department or the Russian immediately embassy responded to a request for comment.
The State Department computer system has been bedeviled by signs that despite efforts to lock them out, the Russian hackers have been able to reenter the system. One official says the Russian hackers have “owned” the State Department system for months and it is not clear the hackers have been fully eradicated from the system.
As in many hacks, investigators believe the White House intrusion began with a phishing email that was launched using a State Department email account that the hackers had taken over, according to the U.S. officials.
Director of National Intelligence James Clapper, in a speech at an FBI cyber-conference in January, warned government officials and private businesses to teach employees what “spear phishing” looks like.
“So many times, the Chinese and others get access to our systems just by pretending to be someone else and then asking for access, and someone gives it to them,” Clapper said.
The ferocity of the Russian intrusions in recent months caught U.S. officials by surprise, leading to a reassessment of the cybersecurity threat as the U.S. and Russia increasingly confront each other over issues ranging from the Russian aggression in Ukraine to the U.S. military operations in Syria.
The attacks on the State and White House systems is one reason why Clapper told a Senate hearing in February that the “Russian cyber-threat is more severe than we have previously assessed.”
Read the rest of the story on CNN…

Donald Trump
THE PROPHECY NEWS PODCAST: Trump’s Iran War Is The Perfect Storm Of Economic Collapse, Homeland Vulnerability, And Potential 4th Of July Enemy Strike

As July 4th Approaches, Trump’s Iran War Leaves America Exposed To Economic Ruin, Infrastructure Attacks, And Foreign Retaliation
Donald Trump’s war with Iran is not merely a foreign-policy crisis. It is now a domestic economic crisis, a homeland-security crisis, and a national-strength crisis rolled into one. The damage is no longer theoretical. Oil has surged above $110 a barrel, gas prices have climbed, inflation pressure is rising again, bond markets are wobbling, and Americans are being forced to pay for a war they did not ask for, cannot afford, and have not been given a convincing explanation for. Recent reporting says Americans have already absorbed more than $40 billion in added fuel costs since the war began, about $316 per household, with higher costs spreading into food, travel, shipping, and consumer goods.
“When the righteous are in authority, the people rejoice: but when the wicked beareth rule, the people mourn.” Proverbs 29:2 (KJB)
On this episode of the Prophecy News Podcast, Trump’s Iran War is doing what reckless wars always do, it’s draining the American people, spiking energy prices, reviving inflation, shaking the markets, and handing our enemies a wider target set. While Trump talks tough overseas, the homeland is being left exposed to cyberattack, proxy retaliation, and symbolic violence at the very moment America prepares to celebrate July 4th. Whether the next blow comes through oil, markets, infrastructure, or a terror-style attack, the truth is plain, this war is not making America stronger. It is making America weaker, poorer, and more vulnerable. Trump promised America First, but his Iran War has produced America Exposed — exposed at the pump, exposed in the markets, exposed in cyberspace, and exposed on the homeland. Today we ask the question, has all this come about through Trump’s massive ego and legendary hubris? Has it come about through incompetence and inability? Or… is what we’re watching the actual plan the Deep State has had since the day they shot Trump’s right ear in Butler, Pennsylvania? These are the tough questions we will attempt to answer today on this edition of the Prophecy News Podcast!
Study Helps And Links For Today’s Podcast
- Bibles Behind Bars Gets Open Door At Williamson County Jail To Send Cases Of King James Bibles After One Mother Asked For Just One Bible For Her Son
- Trump Naively Calls Xi A ‘Good Friend’ While China’s Communist Strongman Invokes The ‘Thucydides Trap’ As A Taunt To The Rising Power Of The East
- The Appointment By Trump Of Bilderberg Group Operative Kevin Warsh To The Federal Reserve Shows How Deep The Global Financial Control System Runs
We Are Broadcasting Live Four Days A Week
-
The BIBLE BELIEVERS Sunday Service
Every Sunday morning, from 11:00 AM – 12:30 PM EST, we invite you to join us live and in-person at the Bible Believers Church here inside the NTEB Bookstore in Palatka where we lift up the Lord Jesus Christ in psalms, hymns and spiritual songs, and preach a message from the pages of the King James Authorized Version Holy Bible.
OUR MOST RECENT SUNDAY SERVICE VIDEO: The Soundtrack Of The World
• The RIGHTLY DIVIDING Radio Bible Study
Every Sunday evening from 7:00 – 9:00 PM EST, we offer an in-depth rightly dividing and dispensationally correct rocket ride through the preserved word of God as found within the pages of the King James Holy Bible.
- SUNDAY NIGHT: Our original Sunday Night Radio Bible Study, it’s from 7:00 – 9:00 PM EST, and we have praise, singing, testimony and of 90-minute King James Bible study. All our King James bible study programs are archived here.
• The NTEB PROPHECY NEWS PODCAST Hour
Every Monday and Friday afternoons from Noon to 1:30 PM EST, we examine breaking news and current events in light of bible prophecy.
- MONDAY AT NOON: Every Monday at Noon we review all the latest news and events related to bible prophecy, and examine what is happening in light of what is written. If you miss the live show, all of our Prophecy News Podcast programs are archived here.
- FRIDAY AT NOON: Friday at Noon we review all the latest news and events related to bible prophecy, and examine what is happening in light of what is written. If you miss the live show, all of our Prophecy News Podcast programs are archived here.
Your Generous Donations Make These Live King James Radio Bible Studies & Prophecy News Podcasts Possible!
HOW TO DONATE: Click here to view our WayGiver Funding page
Listen to What Our Donation Angels Have to Say About the Ministry of Now The End Begins
- “You are truly an end time ministry and I appreciate how our Precious Lord is using you to educate his very own flock. There is a lot of confusion , but your ministry is putting scripture in the right prospective. Thank-you so so much Geoffrey S Grider for standing firm and putting in a lot of hours of your time. God Bless You , also your Ministry and your family. IN JESUS MIGHT NAME.” T. Muto
- “Jesus. I am now 64 years old and never in all the years I’ve been a Christian was I able to grow in the Lord as much as I have in the last past year. All because of our blessed brother’s work Geoffrey Grider who as the bravery of standing fast forward without fear of claiming the truth of God by the power of his love in Jesus Christ. May God bless you abundantly to the end my dear brother… ROMANS: 8: 36,37,38” Mireille Anderson
- “I met you at the car dealership earlier this year. We spoke briefly, then you handed me a card and told me to check out the website. You left. A few minutes later, you returned to tell me not to forget to look up the website. I told you…” I already did. I already subscribed.” In that short time we spoke, I experienced from you…a total stranger…peace, joy, kindness, gentleness, compassion, and love. I am convinced that God sent you to share the Good News that Jesus Christ is our Lord and Savior. For that, and for the work you are doing for the Kingdom of God, I say…Thank you and God Bless You.” Sonia Merced
- “I really enjoy the emails and Bible studies! I haven’t found a church and enjoy your services very much! Be blessed brother!” Marcia Mann
- “You and your organization are on the front lines in the Battle For Truth…. current events, end times, and trying to awaken a sleeping Laodicean Church. Thank you brother for fighting for us and all your teaching and insight God bless…” Daniel Cartrette
- I just want to thank you for the teachings you give every Sunday night on radio. You are such a blessing to me. I absolutely love your way of teaching the scriptures. I don’t have a church where I can have fellowship and teaching, so you have been my teacher for many months now. Thanks God you are there for all of us who have no church to go to. I pray that the Lord will bless you abundantly in your ministry, and your loved ones too. You are such a blessing to me, and many others, in these last days before the rapture. Thank you so much Geoffrey, from the bottom of my heart. May the Lord keep you, until He comes back for us. You are in my prayers.” Donald Godin
- “Thank you for the work you are doing brother. Your page and your testimony were a blessing to me this morning as I came across it for the first time. Thank you for the reality of your testimony and what God has done for you in introducing you to Jesus our Lord. God has brought me, in salvation, to Himself as well, through His love and mercy and grace in salvation. How can we praise Him enough? How can we not share this good news!? I pray this day for God’s blessing on your ministry that He may save many souls through the work He has called you to. Isaiah 40:31 (KJV)” Mark and Melissa
- “Love the Sunday night bible study. I want to support someone who has the passion for the lost like Geoffrey does and rightly divides the word of God. God bless you.” Teresa Carey
- “I give because not many news outlets are brave enough or Godly enough to tell these stories from a Christian’s point of view. I see stories here that will not be seen anywhere else.” William Grayshaw
- “It’s hard to find solid biblical teaching in America these days. It’s a blessing to be able to take part in a ministry financially without being concerned about false teaching. All glory to God! God bless!” Maximilian Swan
- “I donate because you are reporting the truth about the increasing wickedness of our time, as God’s word foretold. In so doing we are reminded to “Keep looking up” as we wait in joyful hope for the Lord’s coming, Maranatha! ” Anthony Sloane
- “Geoffrey has the best End Times News out there. I have been receiving his emails for years now and always enjoy his Sunday night messages although I don’t always think exactly as he thinks. We are all in this “boat of life” together and as I come to the end of my life’s journey here, I am more aware of Jesus’s call for us to be one as He and the Father are One.” Deborah Cleaveland
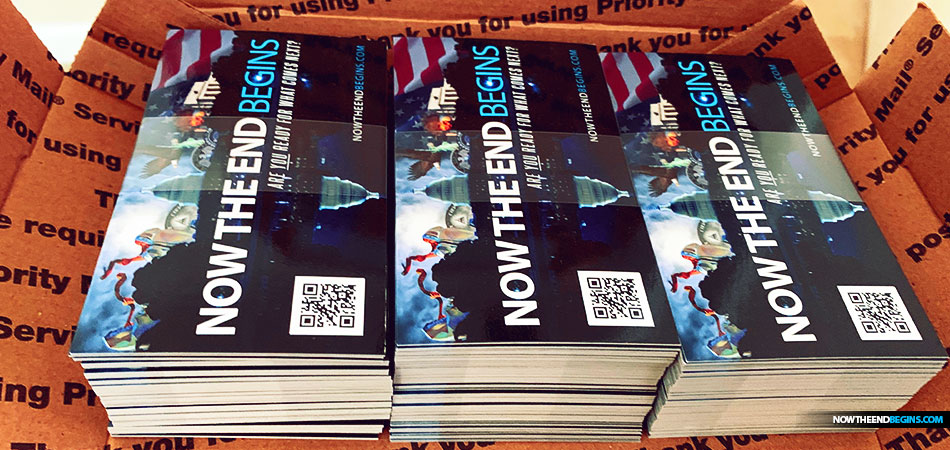
STREET-TESTED NTEB GOSPEL TRACTS:
This is the official gospel tract of NTEB, used here on the streets of Saint Augustine and sent around the world as they are purchased through our website. We ask you to prayerfully consider supporting the work of Now The End Begins by purchasing a box of these full-color, high-quality gospel tracts. Thank you in advance!
But whatever you do, don’t do nothing. Time is short and we need your help right now. The Lord has given us an open door with a tremendous ‘course’ for us to fulfill that will create an excellent experience at the Judgement Seat of Christ. Please pray for our efforts, and if the Lord leads you to donate, be as generous as possible. The war is REAL, the battle HOT and the time is SHORT…TO THE FIGHT!!!
“Looking for that blessed hope, and the glorious appearing of the great God and our Saviour Jesus Christ;” Titus 2:13 (KJB)
“Thank you very much!” – Geoffrey, editor-in-chief, NTEB
Headline News
NTEB RADIO BIBLE STUDY: The Reason Why The People Who Get The Victory Over Antichrist In The Tribulation Will Sing The Song Of Moses From Exodus 15
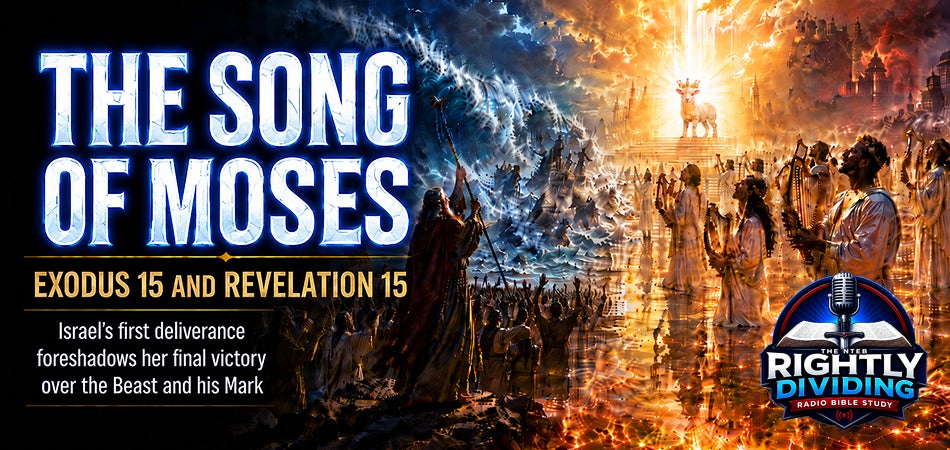
The Same God Who Drowned Pharaoh In The Red Sea Will Destroy Antichrist As Israel Sings The Song Of Moses And The Lamb In Revelation 15
Revelation 15 is one of the clearest places in the Bible where the Holy Spirit deliberately connects Israel’s first great national deliverance with her final deliverance in the time of Jacob’s trouble. In Exodus 15, Moses and the children of Israel sang after the LORD overthrew Pharaoh and his armies in the Red sea; in Revelation 15, those who got the victory over the Beast, his image, his mark, and the number of his name sing “the song of Moses the servant of God, and the song of the Lamb.” That is not Church Age language, and it is not vague devotional poetry. It is Jewish, prophetic, dispensational truth.
“And they sing the song of Moses the servant of God, and the song of the Lamb, saying, Great and marvellous are thy works, Lord God Almighty; just and true are thy ways, thou King of saints.” Revelation 15:3 (KJB)
On this episode of Rightly Dividing, Pharaoh was a type of Antichrist, Egypt was a type of the world system, and the Red sea deliverance was a picture of God bringing His people through judgment while destroying the enemy that sought to enslave them. What began with Moses in Exodus will be brought to its full prophetic conclusion under Jesus Christ, the Lamb, in Revelation. The victory in Revelation 15 is not measured by earthly survival, but by faithfulness to God in the face of the Beast’s global worship system. These Tribulation saints refuse the mark, refuse the image, refuse the Beast’s name and number, and though many of them are killed, heaven records them as victorious. That is Bible victory. The world says victory is keeping your place in the system, protecting your buying and selling, and bowing just enough to survive. God says victory is refusing the Antichrist and standing true to the Lamb. Just as Israel stood on the other side of the Red sea and sang after Pharaoh’s defeat, these overcomers stand on the sea of glass mingled with fire and sing before the final vials of wrath are poured out. The same LORD who judged Egypt will judge the kingdom of the Beast, and the same God who gave Moses a song of deliverance will give Israel’s final remnant a song of triumph before the coming Kingdom.
Study Helps And Links For Tonight’s Bible Study
- The Coming World Government Will Raise The Jews And Israel Above All The Other Nations On Earth With Jesus Christ Ruling On The Throne Of David In Jerusalem
- The Idea That We Are Now Living In Satan’s ‘Little Season’ From Revelation 20 Is Just Another End Times Smokescreen To Divert You From Bible Truth
- Why Are None Of The Celebrity Church Pastors Warning The Jews And Israel About The Coming Time Of Jacob’s Trouble That’s Written In The Prophets?
- Bibles Behind Bars Gets Open Door At Williamson County Jail To Send Cases Of King James Bibles After One Mother Asked For Just One Bible For Her Son
• The BIBLE BELIEVERS Sunday Service
Every Sunday morning, from 11:00 AM – 12:30 PM EST, we invite you to join us live and in-person at the Bible Believers Church here inside the NTEB Bookstore in Palatka where we lift up the Lord Jesus Christ in psalms, hymns and spiritual songs, and preach a message from the pages of the King James Authorized Version Holy Bible.
OUR MOST RECENT SUNDAY SERVICE VIDEO: The Soundtrack Of The World
• The RIGHTLY DIVIDING Radio Bible Study
Every Sunday evening from 7:00 – 9:00 PM EST, we offer an in-depth rightly dividing and dispensationally correct rocket ride through the preserved word of God as found within the pages of the King James Holy Bible.
- SUNDAY NIGHT: Our original Sunday Night Radio Bible Study, it’s from 7:00 – 9:00 PM EST, and we have praise, singing, testimony and of 90-minute King James Bible study. All our King James bible study programs are archived here.
• The NTEB PROPHECY NEWS PODCAST Hour
Every Monday and Friday afternoons from Noon to 1:30 PM EST, we examine breaking news and current events in light of bible prophecy.
- MONDAY AT NOON: Every Monday at Noon we review all the latest news and events related to bible prophecy, and examine what is happening in light of what is written. If you miss the live show, all of our Prophecy News Podcast programs are archived here.
- WEDNESDAY: Every Wednesday we do our Midweek Update, to keep you informed of breaking news. Unlike the other two podcasts, this is a pre-recorded program.
- FRIDAY AT NOON: Friday at Noon we review all the latest news and events related to bible prophecy, and examine what is happening in light of what is written. If you miss the live show, all of our Prophecy News Podcast programs are archived here.
Your Generous Donations Make These Live King James Radio Bible Studies Possible!
On our Sunday and Wednesday night radio bible study, we are preaching and teaching the gospel of the grace of God, rightly divided and dispensationally correct, to a truly global audience who is hungry for the word. These programs would not be possible without your generous support. Listen to just a few of the recent comments we have gotten:
- I thanked God for sending to your website in 2015 , I live in the South of France near Nice and let me tell you here there isn’t any Bible Believing church at all, the sad reality of France is that is full of freemasons and Muslims. You came to me at the time I was going to take my own life because of my job. You’re anointed person and I pray for you, family and ministry because you’re a blessing to all of us. May God bless you always. I know I’ll meet you in heaven one day. Lots of Love from your sister in Christ, Paula.
- “Hi Geoffrey and staff, Today is my one year anniversary that I got saved on your podcast! I am now a KJB only, I threw away my other two versions I had. I was shocked to learn of the differences and how the new versions twist the words of God, and dilute the message at best. Thank you for the fabulous bible education and fire for the Lord. I donate on your website throughout the year. Thanks for all that you do.” Donna
- “I have been reading on NTEB for about 5 years and listening as I can to your services. If I could list the encouragement, the doctrines, the awareness of what is coming (our blessed hope) but also the last days culture in which I live that you have taught me, this email wouldn’t fit in this letter. Because of you, I am a stronger more equipped soldier for Jesus Christ. Thank you sir for you, your ministry in my life. Faithful to the end because He lives in me.” Ruthie Dennis
- “My name is Carl N from Mumbai, India. My wife Andrea and I have been ardent listeners of your Bible Study and news update podcasts from the very start of the lockdown last year. In fact we make it a point to share these links with our family and friends… many times getting into trouble, as the truth upsets people. We cannot even begin to tell you how this has changed our lives and walk with the Lord. Thank you so much for what you’ve been doing for the Kingdom!! We’ve even switched Bible translations to the KJV. For the last month or so, you’ve been speaking about making end times Bible study materials available. This got us really excited, as we’re eager to use these for our weekly house church group.” Carl N – Mumbai, India
- “I listen to your podcasts often. Very enlightening and I’ve learned a lot. I’m Catholic and followed the Holy Bible throughout my life however, since listening to your podcasts, I’ve learned much more. I recently sent NTEB a small donation. I’d like to do so again in the future. I’ve also signed up for NTEB chatroom. Anyways, I have a downloaded version of KJB on my computer and I follow your Bible Study with my pdf version KJB. You have offered to send out printed version of KJB if requested. If not too much trouble, when you or your staff get the opportunity please send me a copy.” Kevin W – Frankfurt, Germany
- Just wanted to let you know that your ministry is producing fruit. After listening to the studies and church on NTEB, I was motivated to write witness letters along with NTEB gospel tracks to friends from my hometown who I know are not saved. I sent two of the letters to former Catholic priests of mine….I attached the response from him urging me to read the book “Prove It!.” My wife and I have been placing your gospel tracks in different places we visit. This coming Sunday, I am hosting my first Bible study in my house with some people in our neighborhood. Tomorrow evening I have been given a chance to teach the lesson to our youth church group (our church is very Laodicean), and I am going to talk to the youth on end times. Thank you so much for your ministry and encouraging us to get something done for Jesus while we still can! Thomas B
- “The sole purpose of this email to you is to let you know how much we have been blessed by your amazing ministry/website. ‘We’ is my wife and I, in our early forties, 3 kids, professing, churchgoing, bible believing Christians in The Netherlands. Since two months, I listen to your bible studies on Sunday evening, and since this week also to your prophecy podcast. I listen to them in the archives, because of the 6 hour time difference. The shofar and the blessing at 0:30 into the study never fails to make tears in my eyes. We are praying for you, we are praying for your voice, that it lasts in these incredible busy times for you. Listening to your podcasts, you seem to do it effortlessly, talking, scanning the chatbox for questions, diving into the texts, from Genesis to Revelation and everything in between, I love it when you realize after 1:30h into the study, actually a lot more subjects need to be addressed! Thank you for all your work and effort, you are doing an amazing job. Although it all seems effortlessly, I know it is not…Our faith is strengthened by your work and we are able to testify in a better way to the people around us!” Wouter D. van der Wiel – Netherlands
- “Wanted to send you encouragement and thank you for all you are doing!! I’ve been reading from this website for about 5 years and I’ve been on this at least 10 times a day. It’s the most honest prophecy website in history. And you have ministered to me greatly. This lockdown has been amazing as God gets us unto himself and smooths out the paths for us. I was reading devotional from Kenneth Copeland and during that time you had really hit That ministries hard. I was not Word Faith but I was feeding off his teaching. During this time I have removed Kenneth Copeland I wanted to thank you for your exposure of his ministry. Holy Spirit is truly the leader of all truths. The bible study on Bill Gates was tremendous. And I had the same check in my spirit as you did. He’s the guy that gonna lead this one world revolution Amazing times we live in. I’m super excited and living in total victory and peace. Once again thank you for the time you put in your reward in heaven will truly be great. Looking forward to this coming week. My prayer tonight is this …Father send Your Son!! DG
- “Thank you oh so much for sound teaching. I am so thankful and blessed for clicking on your channel. I have been on your Facebook page since 2011 and never subscribed to you-tube channel until today. I loved the live recording of singing, what a delight to hear the joy of the Lord in the voices of the congregation. So wonderful to hear the part about Luke 12:36, that has made my eyebrows furrow when I read and therefore I have always steadfast to not leaning on my own understanding. May God continue to bless you, your family friends and loved ones. All Glory be to Jesus, my Saviour Redeemer and King, Amen.” Susan Anderson
- “Loved this teaching! Presented in a clear contextual manner that was easy to follow along. You connected the dots for me that had previously brought so much confusion, namely the 4th seal covenant, the 5th seal tribulation saints, and the 6th seal 2nd Coming of Christ AFTER the wedding of the Body/Bride of Christ IN HEAVEN. Wow, after 41 years since my being born again by the Holy Spirit in to the Body of Christ, I finally have the answers to end the confusion. What joy and peace has flooded my heart! Thank you for this encouraging teaching of the Word.” SB
- “I am from Sri Lanka and listen to the radio Bible study every week.” Nihal Perera
Nothing thrills my soul like teaching the word of God, it is what the Lord called me to do 29 years ago, and Now The End Begins is the vehicle in which I am able to do it. How exciting it is to be able to teach the Bible to tens of thousands of people per year. Like I told you with the first post of 2020, I have dedicated myself now full-time to NTEB, and it is only through your generous support that such a thing is possible.
HOW TO DONATE: Click here to view our WayGiver Funding page
Listen to what our donation angels have to say about the ministry of Now The End Begins
- “You are truly an end time ministry and I appreciate how our Precious Lord is using you to educate his very own flock. There is a lot of confusion , but your ministry is putting scripture in the right prospective. Thank-you so so much Geoffrey S Grider for standing firm and putting in a lot of hours of your time. God Bless You , also your Ministry and your family. IN JESUS MIGHT NAME.” T. Muto
- “Jesus. I am now 64 years old and never in all the years I’ve been a Christian was I able to grow in the Lord as much as I have in the last past year. All because of our blessed brother’s work Geoffrey Grider who as the bravery of standing fast forward without fear of claiming the truth of God by the power of his love in Jesus Christ. May God bless you abundantly to the end my dear brother… ROMANS: 8: 36,37,38” Mireille Anderson
- “I met you at the car dealership earlier this year. We spoke briefly, then you handed me a card and told me to check out the website. You left. A few minutes later, you returned to tell me not to forget to look up the website. I told you…” I already did. I already subscribed.” In that short time we spoke, I experienced from you…a total stranger…peace, joy, kindness, gentleness, compassion, and love. I am convinced that God sent you to share the Good News that Jesus Christ is our Lord and Savior. For that, and for the work you are doing for the Kingdom of God, I say…Thank you and God Bless You.” Sonia Merced
- “I really enjoy the emails and Bible studies! I haven’t found a church and enjoy your services very much! Be blessed brother!” Marcia Mann
- “You and your organization are on the front lines in the Battle For Truth…. current events, end times, and trying to awaken a sleeping laodicean Church. Thank you brother for fighting for us and all your teaching and insight God bless…” Daniel Cartrette
- “I’m a KJB believer. We’re so close to being “caught up together with them in the clouds, to meet the Lord in the air; and so shall we ever be with the Lord. I have many lost family who don’t want the truth, including my husband & son. I’ve been banned from seeing my grandsons since I comforted the 4 1/2 year old with sharing Jesus loving the little children & telling him about the one who created him last he stayed overnight March 3rd. He was so excited to hear about Jesus! His dad (my son) was angry that I told him & wants me to apologize. I never will do so. If my own family won’t hear, I know there’s others searching for the truth. My heart grieves for all the lost who will spend eternity in hell if they reject the Lord Jesus Christ, the expectant hope of the world. He is not willing that any should perish. God bless your ministry, Geoffrey! (I continue to pass out your tracts & you’re on my prayer list!)” LouAnn Benham
- “Love the Sunday night bible study. I want to support someone who has the passion for the lost like Geoffrey does and rightly divides the word of God. God bless you.” Teresa Carey
- “I give because not many news outlets are brave enough or Godly enough to tell these stories from a Christian’s point of view. I see stories here that will not be seen anywhere else.” William Grayshaw
HOW TO DONATE: Click here to view our WayGiver Funding page
STREET-TESTED NTEB GOSPEL TRACTS:
This is the official gospel tract of NTEB, used here on the streets of Saint Augustine and sent around the world as they are purchased through our website. We ask you to prayerfully consider supporting the work of Now The End Begins by purchasing a box of these full-color, high-quality gospel tracts. Thank you in advance!
But whatever you do, don’t do nothing. Time is short and we need your help right now. The Lord has given us an open door with a tremendous ‘course’ for us to fulfill that will create an excellent experience at the Judgement Seat of Christ. Please pray for our efforts, and if the Lord leads you to donate, be as generous as possible. The war is REAL, the battle HOT and the time is SHORT…TO THE FIGHT!!!
“Looking for that blessed hope, and the glorious appearing of the great God and our Saviour Jesus Christ;” Titus 2:13 (KJB)
“Thank you very much!” – Geoffrey, editor-in-chief, NTEB
HOW TO DONATE: Click here to view our WayGiver Funding page
Headline News
THE BIBLE BELIEVERS SUNDAY SERVICE: The Soundtrack Of The World
The First Musician Came From Cain’s Line, And The Last Musicians Are Silenced In Babylon When God Judges The Soundtrack Of The World System
From the very beginning of the Bible, music is presented not as a harmless background feature of human life, but as something deeply connected to worship, culture, rebellion, and spiritual direction. After Cain goes out from the presence of the LORD, his descendants begin building the first city, developing culture, and producing the first human musician. This is the “beating heart” of the 7 Mountains Mandate from the New Apostolic Reformation. The first song mentioned in the Bible is the song of Moses in Exodus 15, and the last song mentioned in the Bible is the song of Moses found in Revelation 15. There is a soundtrack of the world that comes from Cain, and there are the songs of God that come from Heaven. If you are going to have the right music, then you need to find the right City first.
“For he looked for a city which hath foundations, whose builder and maker is God.” Hebrews 11:10 (KJB)
SUNDAY SERVICE STUDY NOTES: The Soundtrack of the World
The Soundtrack Of The World
Cain Leaves The Presence Of The LORD
Cain’s judgment did not produce repentance. Instead of seeking mercy, Cain went out from the presence of the LORD and began life in exile. That is the beginning of man’s organized world-system apart from God. And from the very beginning of that first city, music begins to play as a soundtrack.
“And Cain went out from the presence of the LORD, and dwelt in the land of Nod, on the east of Eden.” Genesis 4:16 (KJB)
This is the first major step: separation from God. Before Cain builds, before his line develops culture, before music appears, Cain first departs from the presence of the LORD.
The order matters: departure from God → city-building → culture → music → violence → judgment
Cain’s world is not built on faith, sacrifice, blood atonement, or obedience. It is built by a man who refused to do things God’s way.
Application
Not every successful civilization is blessed of God. Not every cultural achievement is spiritual. Man can build cities, produce art, develop music, advance technology, and organize society while being completely separated from the LORD. The first city in the Bible does not begin with worship. It begins with Cain. It is this mess that NAR seeks to control through the 7 Mountains Mandate. The seven mountains are: Education, Religion, Family, Business, Government, Arts & Music, and the Media.
Closing Challenge
Be careful not to confuse civilization with righteousness. A world can be educated, musical, artistic, wealthy, and technically advanced — and still be east of Eden, outside the presence of God. Christians are not called to take control of the 7 Mountains, they’re to call lost sinners to come out of it.
“And I heard another voice from heaven, saying, Come out of her, my people, that ye be not partakers of her sins, and that ye receive not of her plagues.” Revelation 18:4 (KJB)
Cain Builds The First City
The first city in the Bible is built by the first murderer. Cain names it after his son Enoch, not after the LORD. This is man making a name for himself in a fallen world.
“And Cain knew his wife; and she conceived, and bare Enoch: and he builded a city, and called the name of the city, after the name of his son, Enoch.” Genesis 4:17 (KJB)
Cain’s city becomes the prototype of the world-system: organized human life without submission to God. It is not merely bricks and buildings. It is the beginning of man’s attempt to create security, identity, culture, legacy, and permanence apart from the LORD.
This is the spirit that later appears at Babel:
“And they said, Go to, let us build us a city and a tower, whose top may reach unto heaven; and let us make us a name, lest we be scattered abroad upon the face of the whole earth.” Genesis 11:4 (KJB)
Cain names his city after his son. Babel says, “let us make us a name.” Same spirit. Same rebellion. Same self-exalting civilization. Ezekiel shows us God’s city that will exist in the Millennium.
“It was round about eighteen thousand measures: and the name of the city from that day shall be, The LORD is there.” Ezekiel 48:35 (KJB)
Application
The world is always trying to make a name for itself. It builds cities, systems, empires, religions, music industries, entertainment kingdoms, and commercial networks — but without God, it is still Cain’s city.
Closing Challenge
Ask yourself this: am I building for the LORD, or am I building something to preserve my own name? Moravian church bishop Count Nikolaus Von Zinzendorf famously said “Preach the gospel, die, and be forgotten”. And that’s good advice. Peter says “Humble yourselves therefore under the mighty hand of God, that he may exalt you in due time:” 1 Peter 5:6 (KJB)
Music Appears In Cain’s Line
The first human musician mentioned in the Bible is Jubal, a descendant in Cain’s line.
“And his brother’s name was Jubal: he was the father of all such as handle the harp and organ.” Genesis 4:21 (KJB)
This does not mean music itself in and of itself is evil. God later uses music in worship, praise, prophecy, and spiritual rejoicing. But the first mention of human music is not in the tabernacle, not in the temple, not among the sons of Levi, and not in the Psalms. It is in Cain’s line. That is prophetically instructive. Music appears early in the development of man’s world apart from God. Alongside city-building, livestock enterprise, metallurgy, and violence, music becomes part of fallen man’s culture.
“And Zillah, she also bare Tubalcain, an instructer of every artificer in brass and iron: and the sister of Tubalcain was Naamah.” Genesis 4:22 (KJB)
Cain’s line produces culture, craftsmanship, industry, music, and metalwork. But it does not produce worship of the LORD.
“Woe to them that are at ease in Zion, and trust in the mountain of Samaria, which are named chief of the nations, to whom the house of Israel came! That chant to the sound of the viol, and invent to themselves instruments of musick, like David; Therefore now shall they go captive with the first that go captive, and the banquet of them that stretched themselves shall be removed. The Lord GOD hath sworn by himself, saith the LORD the God of hosts, I abhor the excellency of Jacob, and hate his palaces: therefore will I deliver up the city with all that is therein.” Amos 6 (KJB)
Application
Music is powerful because it moves the heart. It can carry doctrine, emotion, rebellion, sensuality, worship, sorrow, joy, idolatry, or praise. The question is not merely, “Does it sound good?” The question is, “What spirit does it carry, what truth does it teach, and whom does it glorify?”
Closing Challenge
Do not judge music only by talent, beauty, popularity, or emotional effect. Cain’s line had music before it had worship.
Lucifer Was Connected With Music Before Jubal
Before Jubal ever handled the harp and organ, the anointed cherub appears to have had musical workmanship connected with him in the day he was created.
“Thou hast been in Eden the garden of God; every precious stone was thy covering, the sardius, topaz, and the diamond, the beryl, the onyx, and the jasper, the sapphire, the emerald, and the carbuncle, and gold: the workmanship of thy tabrets and of thy pipes was prepared in thee in the day that thou wast created.” Ezekiel 28:13 (KJB)
This passage addresses the king of Tyrus, but the language clearly reaches beyond an earthly ruler. He was “in Eden the garden of God.” He was “created.” He was connected with “tabrets” and “pipes.”
Music is not a small thing in Scripture. It is deeply spiritual.
Lucifer’s fall was rooted in pride and self-exaltation:
“How art thou fallen from heaven, O Lucifer, son of the morning! how art thou cut down to the ground, which didst weaken the nations!” Isaiah 14:12 (KJB)
“For thou hast said in thine heart, I will ascend into heaven, I will exalt my throne above the stars of God: I will sit also upon the mount of the congregation, in the sides of the north: I will ascend above the heights of the clouds; I will be like the most High.” Isaiah 14:13 (KJB)
That same self-exalting spirit shows up in Babel: “let us make us a name.”
Application
The devil understands music. He understands beauty. He understands atmosphere. He understands emotional movement. He understands how to use sound to influence worship, doctrine, culture, and rebellion.
This is why music must be tested spiritually, not merely enjoyed emotionally.
Closing Challenge
The issue is not whether music moves you. The issue is where it moves you.
Babel Continues The Spirit Of Cain’s City
Babel does not physically descend from Cain’s preserved genealogy, because the Flood comes between Cain’s world and the post-Flood nations. After the Flood, Babel arises through Nimrod, from the line of Ham.
“And the sons of Ham; Cush, and Mizraim, and Phut, and Canaan. And the sons of Cush; Seba, and Havilah, and Sabtah, and Raamah, and Sabtecha: and the sons of Raamah; Sheba, and Dedan. And Cush begat Nimrod: he began to be a mighty one in the earth. He was a mighty hunter before the LORD: wherefore it is said, Even as Nimrod the mighty hunter before the LORD. And the beginning of his kingdom was Babel, and Erech, and Accad, and Calneh, in the land of Shinar.” Genesis 10:6-10 (KJB)
So physically, Babel is not traced through Cain. But spiritually and typologically, Babel carries forward the way of Cain. Cain built the first city. Nimrod builds the first kingdom-city system. Cain went out from the presence of the LORD. Babel organizes mankind in collective rebellion against the command of God.
“And they said, Go to, let us build us a city and a tower, whose top may reach unto heaven; and let us make us a name, lest we be scattered abroad upon the face of the whole earth.” Genesis 11:4 (KJB)
Babel is Cain’s city expanded into a global religious-political project.
Application
The world-system always wants unity without truth, religion without obedience, culture without holiness, and heaven without the God of heaven.
That is Babel.
Closing Challenge
Beware of any movement that promises unity while rejecting the word of God. Babel was unified, but God still judged it.
Babylon Is The Final Form Of Cain And Babel’s System
Babylon the great in Revelation is the final prophetic form of the same system that began in seed form with Cain’s city and was organized nationally at Babel.
- Cain gives us the first city.
- Babel gives us the first kingdom-city rebellion.
- Babylon the great gives us the final world-system before the Second Advent.
“And there came one of the seven angels which had the seven vials, and talked with me, saying unto me, Come hither; I will shew unto thee the judgment of the great whore that sitteth upon many waters: With whom the kings of the earth have committed fornication, and the inhabitants of the earth have been made drunk with the wine of her fornication. So he carried me away in the spirit into the wilderness: and I saw a woman sit upon a scarlet coloured beast, full of names of blasphemy, having seven heads and ten horns. And the woman was arrayed in purple and scarlet colour, and decked with gold and precious stones and pearls, having a golden cup in her hand full of abominations and filthiness of her fornication: And upon her forehead was a name written, MYSTERY, BABYLON THE GREAT, THE MOTHER OF HARLOTS AND ABOMINATIONS OF THE EARTH.” Revelation 17:1-5 (KJB)
Babylon is religious. Babylon is political. Babylon is commercial. Babylon is seductive. Babylon is wealthy. Babylon is global. Babylon is anti-God.
Revelation 18 shows her commercial greatness:
“And the merchants of the earth shall weep and mourn over her; for no man buyeth their merchandise any more:” Revelation 18:11 (KJB)
And then, at the end, her music stops:
“And the voice of harpers, and musicians, and of pipers, and trumpeters, shall be heard no more at all in thee; and no craftsman, of whatsoever craft he be, shall be found any more in thee; and the sound of a millstone shall be heard no more at all in thee;” Revelation 18:22 (KJB)
That is a stunning Bible connection.
- The first human musician appears in Cain’s line.
- The last musicians mentioned are silenced in Babylon.
- The world-system begins with music in Genesis 4 and ends with music being judged in Revelation 18.
Application
Babylon’s music represents more than entertainment. It is the sound of a world celebrating itself while standing under the judgment of God. It is the music of commerce, pleasure, seduction, religion, idolatry, and rebellion. It is the soundtrack of a civilization that made itself rich, intoxicated the nations, and rejected the LORD.
Closing Challenge
When God judges Babylon, He does not merely stop her armies. He unplugs their Jukebox and stops her music.
Godly Music Is Different From Babylon’s Music
The Bible does not condemn music itself. The LORD receives praise, singing, psalms, harps, trumpets, and spiritual songs when they are directed toward Him in truth.
“Serve the LORD with gladness: come before his presence with singing.” Psalm 100:2 (KJB)
“Praise ye the LORD. Sing unto the LORD a new song, and his praise in the congregation of saints.” Psalm 149:1 (KJB)
“And when they had sung an hymn, they went out into the mount of Olives.” Matthew 26:30 (KJB)
“Let the word of Christ dwell in you richly in all wisdom; teaching and admonishing one another in psalms and hymns and spiritual songs, singing with grace in your hearts to the LORD.” Colossians 3:16 (KJB)
So the issue is not music versus no music. The issue is Cain’s music or Christ’s music. The issue is whether the song is serving the world, the flesh and the Devil, or serve the LORD God.
Application
Godly music is not just religious-sounding music. According to Colossians 3:16, it is connected to the word of Christ dwelling richly, teaching, admonishing, wisdom, grace, and the LORD.
That is very different from music designed merely to entertain, seduce, excite, manipulate, or glorify man.
Closing Challenge
A song can mention God and still not be spiritual. The test is whether it lines up with the word of God and glorifies the Lord Jesus Christ.
The Prophetic Pattern
Here is the full pattern:
- Lucifer: music connected with the anointed cherub before his fall.
- Cain: first murderer, departs from the presence of the LORD.
- Cain’s city: first city, built by a rebel.
- Jubal: first human musician, from Cain’s line.
- Babel: first organized kingdom-city rebellion under Nimrod.
- Babylon: final global system of religious, political, commercial, and cultural rebellion.
- Revelation 18: Babylon’s musicians are silenced forever.
This is not accidental. The Bible is showing us that the world-system has always had a soundtrack. It began with a man who went out from the presence of the LORD. It grew into a city. It organized into Babel. It ends as Babylon the great. And when God judges it, the music stops.
Application
The world’s music is often not neutral. It can carry the spirit of Cain, the pride of Lucifer, the rebellion of Babel, and the seduction of Babylon.
But the believer’s song should be different.
“And they sung a new song, saying, Thou art worthy to take the book, and to open the seals thereof: for thou wast slain, and hast redeemed us to God by thy blood out of every kindred, and tongue, and people, and nation;” Revelation 5:9 (KJB)
The world sings about itself. Heaven sings about the Lamb.
Closing Challenge
Make sure your music belongs to the right city. Cain’s city has a song, and Babylon has musicians. But the City of Zion has the Lamb.
Now The End Begins is your front line defense against the rising tide of darkness in the last Days before the Rapture of the Church
- HOW TO DONATE: Click here to view our WayGiver Funding page
When you contribute to this fundraising effort, you are helping us to do what the Lord called us to do. The money you send in goes primarily to the overall daily operations of this site. When people ask for Bibles, we send them out at no charge. When people write in and say how much they would like gospel tracts but cannot afford them, we send them a box at no cost to them for either the tracts or the shipping, no matter where they are in the world. We have a Gospel Billboard program. We are now broadcasting Bible studies, Podcasts and a Sunday Service 5 times a week, thanks to your generous donations. All this is possible because YOU pray for us, YOU support us, and YOU give so we can continue growing.
But whatever you do, don’t do nothing. Time is short and we need your help right now. The Lord has given us an open door with a tremendous ‘course’ for us to fulfill that will create an excellent experience at the Judgement Seat of Christ. Please pray for our efforts, and if the Lord leads you to donate, be as generous as possible. The war is REAL, the battle HOT and the time is SHORT…TO THE FIGHT!!!
“Looking for that blessed hope, and the glorious appearing of the great God and our Saviour Jesus Christ;” Titus 2:13 (KJB)
“Thank you very much!” – Geoffrey, editor-in-chief, NTEB
-
George Soros10 years ago
Proof Of George Soros Nazi Past Finally Comes To Light With Discovery Of Forgotten Interview
-
Election 201610 years ago
DEAD POOL DIVA: Huma Abedin Kept Those Hillary Emails That The FBI Found In A Folder Marked ‘Life Insurance’
-
Election 201610 years ago
Crooked Hillary Campaign Used A Green Screen At Today’s Low Turnout Rally In Coconut Creek FL
-
George Soros10 years ago
SORE LOSER: George Soros Declares War On America As Violent MoveOn.Org Protests Fill The Streets
-
Donald Trump10 years ago
Donald Trump Will Be 70 Years, 7 Months And 7 Days Old On First Full Day In Office As President
-
Headline News10 years ago
If Hillary Is Not Guilty, Then Why Are Her Supporters Asking Obama To Pardon Her? Hmm…
-
Election 201610 years ago
WikiLeaks Shows George Soros Controlling Vote With 16 States Using SmartMatic Voting Machines
-
End Times10 years ago
False Teacher Beth Moore Endorses The Late Term Partial-Birth Abortion Candidate Crooked Hillary