

Massive global uncertainty over US Trump tariffs causing wild fluctuations in the stock market is absolutely related to the coming Mark of the Beast Alarms bells...


Satan will use pure gold in the manufacture of his Mark of the Beast, but God is planning to throw him a curve ball by changing...


President-elect Donald Trump, who takes office on Monday, has promised to usher in a golden age of cryptocurrency. What does it have to do with the...


Christian, the end times are no longer knocking on the door, they have kicked it in and are swarming from all directions as Mohammed bin Salman...


Biometric payment options will soon be everywhere as this lost world moves closer and closer to the 666 Mark of the Beast System. The book of...
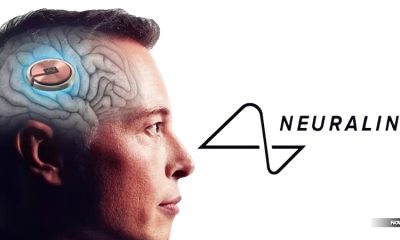

Elon Musk, billionaire founder of Neuralink, said the first human received an implant from the brain-chip startup on Sunday and is recovering well, in a post...


The U.S. Securities and Exchange Commission (SEC) has reportedly approved the first spot bitcoin exchange-traded funds (ETFs), signifying significant progress in the integration of cryptocurrency into...


‘Elon Musk is not just a player that should be regulated by the American government. He’s a global order player, who should probably have a seat...


FEMA in coordination with the Federal Communications Commission (FCC), will conduct a nationwide test of the Emergency Alert System (EAS) and Wireless Emergency Alerts (WEA) today,...


The Mark of the Beast connected to Antichrist comes with something else that’s rarely discussed, and that’s the unholy spirit of the Beast. We recently finished...


The Mark of the Beast of Antichrist includes a name, a number and an image in addition to the mark people are warned against taking for...


The Mark of the Beast of Antichrist includes a name, a number and an image in addition to the mark people are warned against taking for...


The Mark of the Beast of Antichrist includes a name, a number and an image in addition to the mark people are warned against taking for...


The Mark of the Beast of Antichrist includes a name, a number and an image in addition to the mark people are warned against taking for...


We are the generation that will see a cashless society, the Pretribulation Rapture and the Mark of the Beast. It’s all coming, and Elon Musk is...


Alex Blania, CEO of Worldcoin, a company that wants billions of people to scan their irises to create a global system of authentication, says that a...


Whole Foods Markets in the greater Denver area is now taking cashless palm payments through Amazon One at 11 of their store locations. Remind you of...


A UK government adviser is confident any future pandemic lockdown and compulsory mask edicts will be met with compliance because people have learnt a new behaviour...


Apple announced its mixed-reality headset, the Vision Pro, on Monday during its WWDC developer conference. The $3,499 headset is its first major new product since the Apple Watch...


Elon Musk gets approval from the FDA for his Neuralink brain chip that will function as a ‘bridge’ to the soon-coming Mark of the Beast In...


The Federal Reserve Bank of New York’s Innovation Center, or NYIC, announced that it would be launching a 12-week proof-of-concept pilot for a central bank digital...


Elon Musk went full Satan this Halloween by wearing ‘The Devil’s Champion’ costume which featured an upside-down cross inside the head of Baphomet Just in case...


Arnie Szoke is the first Brit to get microchipped with a bank card implant from biotech company Walletmor — letting him pay with just his right...


Remember that Jesus warns us that the very first sign of the beginning of sorrows, a time that has its doctrinal fulfillment after the Pretribulation Rapture...